patches
Critical Security Threat
Wed, 22/07/2015 - 4:01pm — jethro
A critical security threat was announced and an out of sequence patch released yesterday by Microsoft.
It affects ALL pcs running Vista, Windows7, 8, 8.1 and Windows RT.
There is specific news here if you want more http://www.cnet.com/news/microsoft-rushes-emergency-security-fix-for-versions-of-windows/
And the technical stuff is here https://technet.microsoft.com/library/security/MS15-078?f=255&MSPPError=-2147217396#ID0EKIAE
Please patch all your PCs and Servers immediately.
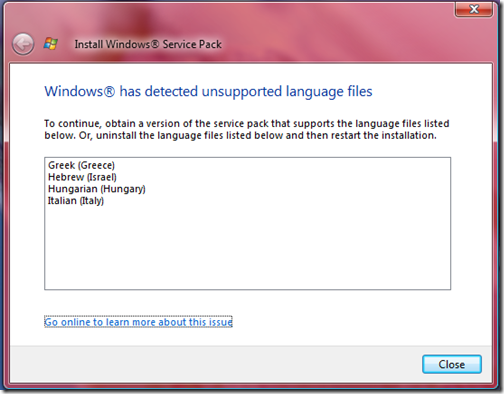
Why I was not getting Vista Service Pack 2 offered to me
Fri, 03/07/2009 - 11:36am — jethroSo I had authorised Vista SP2 in my WSUS server and i had noticed other machines on my network installing it. But my machine didn’t show it up in the updates to install list. I eventually went and downloaded the full standalone version. In the meantime i came across this post by Susan Bradley about having important updates not installed stopping SP2 from being available. I went and checked but that wasnt my problem.
When i tried to actually run the SP2 download I got this message:
I went into the control panel to Regional and Language Settings
Security vulnerabilities announced in Microsoft Excel and Drupal
Thu, 26/02/2009 - 11:43am — jethroSecurity vulnerabilities were announced today in Microsoft Excel and also in Drupal.
 See the Official MS security advisory (968272), and the explanation by ars technica.
See the Official MS security advisory (968272), and the explanation by ars technica.
Our advice for now would be to be EXTREMELY careful when opening any Excel spreadsheet, Word document or PowerPoint file that is emailed to you. Rule of thumb – if you don’t know the person who set you a file (any file) NEVER open it. If you weren’t expecting the file from someone you do know then email or call them and ask them if they sent you it and if so what it is BEFORE opening it. I trust that MS will release the appropriate patch shortly.
The Drupal security vulnerabilities have been announced on the Drupal website and upgrades and patches released for both version 5 and 6.
For our Jethro Consultants Web hosting customers this means an immediate patch for those who are on maintenance contracts with us, and for those who are not they pay us by the hour to apply. We get to those as soon as we can. We are also busy upgrading our own websites.
This weeks round up of news and cool web stuff
Fri, 05/12/2008 - 11:31am — jethroLive Mesh announces an update affecting all platforms
Windows Vista SP2 hits the streets today - Sarah has a full list of the enhancements and fixes in Vista SP2
Tony Morgan posts a though provoking piece with 10 reasons why he doesn’t like most Christians. I would agree with them all.
Rodney Olsen posted this cool video about technological and futuristic trends. I have added it here also.




Recent comments
10 years 28 weeks ago
10 years 28 weeks ago
10 years 29 weeks ago
10 years 29 weeks ago
10 years 29 weeks ago
10 years 29 weeks ago
10 years 29 weeks ago
10 years 29 weeks ago
10 years 29 weeks ago
10 years 29 weeks ago